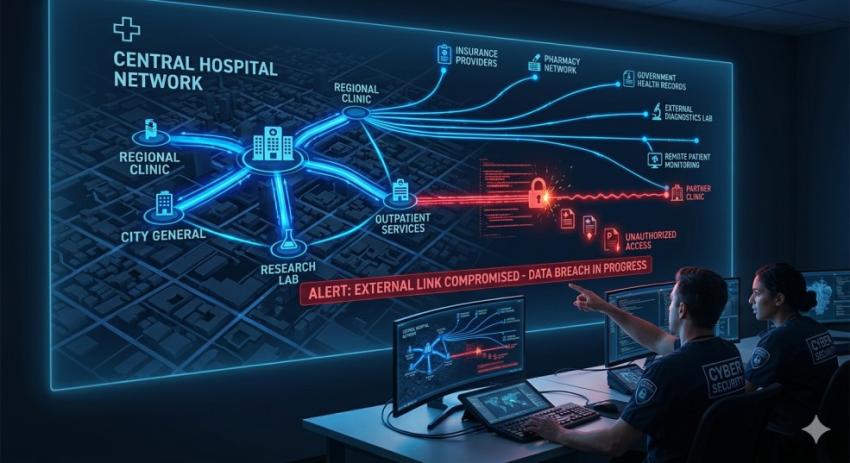
The concept of a healthcare system has changed and there is much more than just hospitals and clinics. It has become more of an ecosystem that consists of multiple partners; such as, billings providers, care coordination agencies, cloud platforms, and data processors. This ecosystem contributes to improvements in efficiency and provides better care for patients, but it also contributes to increasing risks of exposure to breaches, due to the dependence of one partner on a partner's third-party networks for protection against breaches.
A case in point is the recent NYC hospitals data breach of their data. NYC Health and Hospitals Corporation reported that they detected suspicious activities occurring in their own network, but part of the breach was caused by a third-party vendor. This event emphasizes one of the most critical threats to the security of healthcare providers; that they are only as secure as the weakest member of their partner ecosystem.
In the world of healthcare, providers are very dependent upon third-party vendors to manage such things as patient records, and administrative functions on their behalf. These vendors have access to sensitive patient information such as; medical records, insurance information and personal identifiers. The extent to which a vendor has invested in securing its infrastructure is not the same as those of the larger healthcare providers.
Thus, there is a significant risk associated with the use of third-party connections. A breach can occur at a third-party provider regardless of the level of investment being made to secure an individual provider's systems. In many cases, service providers need access to third-party systems to adequately operate, which adds another level of difficulty in eliminating or restricting access to these third-party networks every day.
Perhaps the most alarming aspect of vendor breaches relating to security is how long unauthorized access can take place for. For example, access is reported to have occurred over several months from the end of November to the end of February. Long-term access increases the risk that a tremendous amount of data would be accessed or copied without detection.
Additionally, because the data is made up of sensitive materials, healthcare records are one of the most sought after forms of personal information. Healthcare records can include more than just personal identity information such as your name or social security number. They may have a patient’s entire medical history, treatment history, insurance information, and even biometric data.
One thing that makes medical information so unique compared to financial information (which may have a reset or replacement capability) is that once it has been compromised, it can be used for identity theft, insurance fraud, or even scam targeting individuals who were compromised because of what their medical records contain.
Another difficulty is that all of these incidents occurred in multiple instances. Alongside the core incident, the addition of a separate cybersecurity incident that was related to an individual’s care coordination partner increases the overall impact. This clearly illustrates how interconnected systems create overlapping vulnerabilities, which in turn creates additional points of failure and increased overall risk.
The long-term effects of exposing health and personal information are severe for individuals. The exposure of health and personal information results in potential for financial harm as well as ongoing exposure to fraudulent insurance claims, unauthorized medical services, and abuse of privacy.
For Health Care Providers, this is a wake-up call. Vendor risk management must be a key part of your cybersecurity strategy. These include making a point of conducting thorough security assessments, having restricted access to data, establishing strict security requirements within contracts, and continually monitoring third-party activity.
At the end of the day, the future of health care is dependent on interconnected systems—this also means participating in shared responsibility for each of the systems. Protecting the entire ecosystem—not just each of the systems in the ecosystem—will be important in securing patient information and maintaining trust as security threats continue to develop.