Introduction
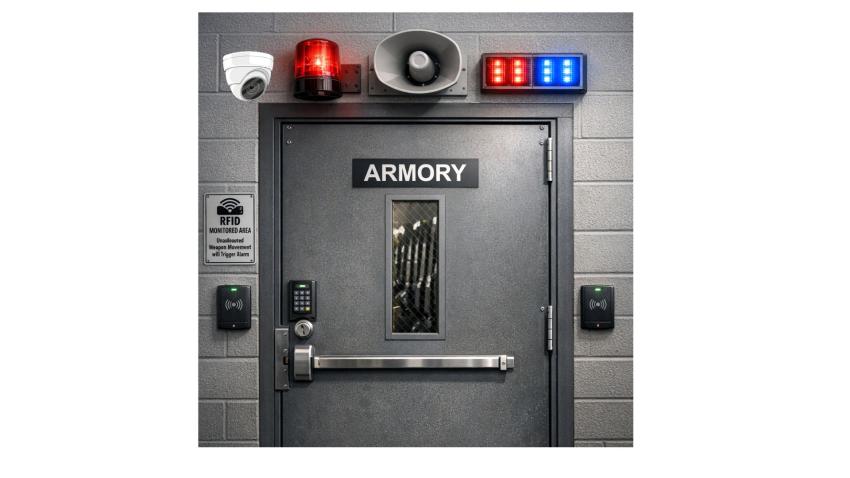
Armory security represents one of the most critical aspects of military and law enforcement operations. One of the main challenges being faced by modern armories is accountability and real-time tracking of weapons. The weapons might have been taken by personnel without proper authorization or intentionally taken to commit some unauthorized acts. Whatever the case may be it becomes a big risk of these weapons fall in wrong hands and are used for anti social and anti national activities. The integration of Closed-Circuit Television (CCTV) surveillance systems with Radio Frequency Identification (RFID) technology creates a comprehensive security framework that addresses these challenges through real-time monitoring, automated tracking, and intelligent threat detection. This integrated approach combines the visual verification capabilities of CCTV systems with the precise asset tracking features of RFID technology, creating multiple layers of security that significantly reduce the risk of unauthorized weapon exits. The system provides continuous monitoring, instant alerts, and comprehensive audit trails essential for maintaining accountability in high-security environments.
CCTV Surveillance Systems
Modern CCTV systems have evolved far beyond simple video recording. Today's intelligent surveillance platforms incorporate:
• AI-Powered Analytics: Advanced algorithms capable of detecting suspicious behavior patterns, unauthorized personnel, and weapon identification
• Real-Time Monitoring: Continuous surveillance with instant alert capabilities
• High-Definition Recording: Crystal-clear video evidence for incident investigation and compliance reporting
• Night Vision Capabilities: 24/7 monitoring regardless of lighting conditions
RFID Technology and Tagging of Weapons with RFID tags
RFID is a wireless technology that uses radio waves to identify and track objects tagged with RFID tags. A typical RFID system contains mainly three components: RFID tags, RFID readers(plus antennas) and central software for data processing and reporting. Each RFID tag contains a unique identifier that can be read remotely by a reader without requiring direct line-of-sight. This capability allows multiple tags to be detected simultaneously, even when they are stored inside racks, cabinets, or containers. The only constraint for UHF (Ultra High Frequency) RFID is that the metal and liquid impacts the reading performance. UHF tags are the ones which are mainly used in armory management operations.
RFID systems can be broadly categorized into passive RFID and active RFID. Passive RFID tags derive power from the reader’s radio signals and are typically used at choke points such as armory doors or issue counters. Active RFID tags, on the other hand, contain a battery and periodically transmit beacon signals, enabling long-range detection and real-time monitoring over large storage areas. Weapon tracking systems mostly use passive RFID tags and we are going to discuss use of these tags in this article.
In RFID enabled Armories, the weapons & other serialized items are tagged with passive RFID tags. These tags are either embedded in weapons grips or attached externally with industrial grade adhesives to withstand harsh conditions such as firing, cleaning and regular maintenance. These tags are commissioned and mapped with serial numbers of weapons in the system. This mapping allows the system and hardware work directly with tagged weapons or items. Once tagged, these items become digitally traceable and any action/activity done with these items is logged in weapon tracking system creating tamper proof audit trail. RFID readers installed at strategic locations automatically monitor the movement of weapons or items. For example, installing RFID readers at exit doors or windows can help in prevention of unauthorized exit of weapons.
Integration of CCTV and RFID to Prevent Un-authorized Exit of Weapons
Security is a primary concern in armory operations, and RFID provides proactive monitoring capabilities that go beyond traditional barcode or manual systems. RFID antennas installed at exit points can detect tagged weapons being removed without proper authorization. If the system cannot associate the weapon with an approved personnel ID, it can automatically trigger alarms, flashing lights, or notifications via email or SMS. Additionally, RFID-based security logs create time-stamped records of all weapon movements. These records can be reconciled with surveillance camera footage to identify responsible individuals in case of discrepancies or security breaches. Passive, unattended monitoring ensures that weapon accountability is maintained even when human supervision is limited
Implementation Framework
Phase#1 - Infrastructure Assessment and Planning
• Evaluate existing security infrastructure
• Identify critical control points and vulnerability areas
• Assess network connectivity and power requirements
• Determine integration points with existing systems
Phase#2 - System Installation and Configuration
• Install fixed readers at strategic locations including entry/exit points, storage areas, and transfer stations
• Configure detection zones to minimize false positives while ensuring complete coverage
• Implement weapon tagging procedures with minimal impact on functionality
• Position cameras for optimal coverage of all RFID detection zones
• Configure AI analytics for unauthorized personnel detection, weapon detection and behavioral analysis
• Establish redundant recording systems for critical areas
Phase#3 - System Integration and Testing
• Configure unified dashboard for monitoring both CCTV and RFID data
• Establish alert protocols and escalation procedures
• Integrate with existing access control and alarm systems
• Conduct thorough testing of all system components
• Verify alert mechanisms and response procedures
• Train personnel on system operation and emergency protocols
Conclusion
The integration of CCTV and RFID technologies represents a significant advancement in armory security capabilities. This comprehensive approach addresses the critical need for real-time monitoring, automated tracking, and immediate threat response while improving operational efficiency and reducing long-term costs.
Success in implementing these integrated systems requires careful planning, adequate investment in both technology and training, and commitment to ongoing maintenance and improvement. Organizations that successfully deploy these systems report dramatic improvements in security posture, operational efficiency, and regulatory compliance.
The future of armory security lies in the continued evolution and integration of these technologies, with emerging capabilities in artificial intelligence, machine learning, and IoT sensors promising even greater security and efficiency gains. Organizations investing in these integrated solutions today position themselves at the forefront of security technology and operational excellence.