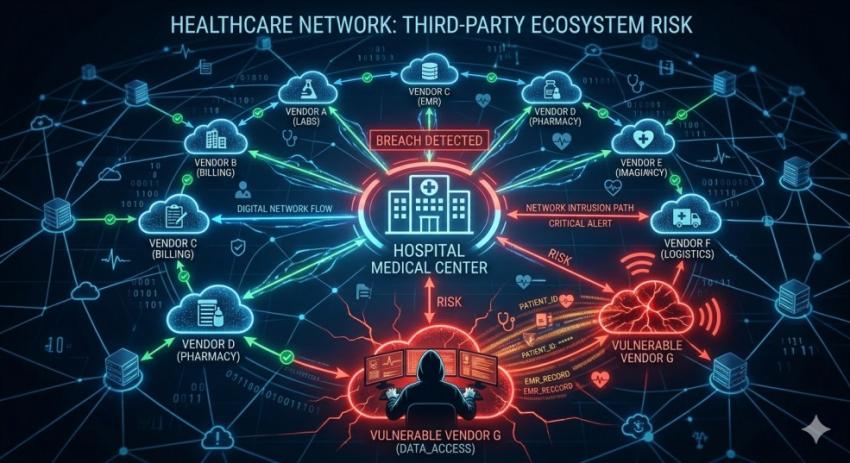
The perception of healthcare providers as the custodians of patient data has changed now that healthcare providers are no longer solely responsible for protecting patient data. Due to the expanding use of digital data and technology, patient data protection now rests with external third parties, such as vendors, consultants, and service providers.
One recent example of an external data breach affecting patient data occurred with the Deaconess Health System (the "healthcare provider") during which a third-party vendor that processed the healthcare provider's patient data was responsible for the data breach. As this event demonstrates, even when a healthcare provider has invested heavily in protecting its own assets and securing its own data, it can be exposed to significant financial (and liability) costs as a result of data breaches that affect external third parties.
The Expanding Role of Third-Party Vendors
A large number of entities are responsible for assisting modern healthcare organizations in managing their administrative and clinical operations. These entities include but are not limited to billing services, e-records vendors, cloud storage services, Release of Information (ROI) service providers, and other third-party service providers. All third parties may have access to the same protected health information (PHI) that healthcare providers use, and, therefore, must use different methods for processing and/or storing that same PHI (e.g., based on systems used).
Outsourcing both increases scalability and efficiency while at the same time providing multiple entry points to sensitive systems. Each new integration can create additional areas of risk, particularly when the vendor’s cybersecurity procedures are inadequate and do not adhere to specified security standards.
Reasons for Increases in Vendor-based Breaches
Vendor-based breaches are on the rise for a number of reasons:
• Patient Data is no longer limited to a single environment and is regularly transferred to various platforms, vendors and cloud environments.
• Vendor Security Practices are not standardized, meaning there are different levels of protection for various vendor types.
• Service Providers do not always give their clients the ability to inspect how they store, manage and share patient data.
• Vendors are prime targets for cyber criminals to exploit since they typically have less stringent security but provide access to large amounts of valuable data.
In Deaconess, the vendor’s cloud-based file-sharing system used for managing patient information requests was hacked, illustrating how a specific operational function, such as responding to record requests, can provide a vulnerability point.
What Makes Healthcare Data So Valuable
Healthcare data is some of the most sensitive and valuable types of information. They include:
-Personal identifiers (name, social security number)
-Medical history and treatment records
-Insurance and billing information
Unlike financial data, which can sometimes be changed quickly (such as when someone gets a new credit card number), medical data is permanent and therefore is very appealing to identity thieves, insurance criminals, and other types of exploitation.
The Challenge of Shared Responsibility
A significant challenge presented in vendor-related breaches is accountability. When a third party has compromised data, it can become unclear who has responsibility between the provider and the vendor. Unfortunately for patients, however, they are affected regardless of the location of the breach event; therefore the following questions must be asked:
-How are vendors vetted prior to onboarding
-What security requirements are included in the contract
-How quickly incidents are detected and reported to the patients
Elevating the Security of Vendors
As organizations have begun to implement stricter vendor management practices to mitigate vendor-related cybersecurity risks, they are:
Conducting regular security audits and compliance checks of each vendor's security practices
Granting vendors access to only that information and only when absolutely necessary for performing their expected duties
Using encryption or other secure means when sharing data with vendors
Requesting all vendors have a written incident response plan in the event their systems become compromised.
Organizations should also ensure that employees are aware of how their data may be shared by different healthcare entities, as well as the risks associated with each one.
Conclusion
The growing incidence of vendor-related data breaches represents a fundamental change in the way organizations manage their overall cybersecurity risk. Cybersecurity risk now extends beyond simply protecting your enterprise; you must also protect the entire ecosystem of integrated systems.
As organizations continue to move towards a digitally-based healthcare ecosystem, it will be crucial for all entities who participate in the data chain to adhere to strong vendor cybersecurity standards to minimize future risks to their operations.